Data Security Offloading: A Guide
Data privacy, confidentiality, and resilience processes often require multiple steps and significant processing power to be implemented into an application. This can be a drag on an already busy application or storage solution.
But what if you could separate the intense implementation and processing of data privacy and resilience from the application itself — without losing any of the benefits of data privacy and resilience? This is the primary purpose of data security offloading.
Below, I’ll describe data security offloading, its benefits, and how a microsharding solution can perform data security functions with minimal performance impact.
What is data security offloading?
Data security offloading is the practice of performing data privacy, confidentiality, and resilience processes through a separate service so that these functions don’t affect the application’s development time or performance.
Many modern applications provide data privacy by taking actions to encrypt and/or decrypt data. However, these actions can have a substantial impact on application design, and they often create a heavy load that affects the application’s performance.
To address this burden of encrypting data in applications, many DevOps and security teams now employ data security offloading. This involves removing encryption duties from the application and instead introducing data security processes before the data reaches its source or storage.
Data security offloading might introduce privacy and resilience processes on a totally separate server or internal hosted service, or it might be handled by a different business unit focused on security rather than application engineering. Either way, the right data security offloading solution can allow teams to achieve robust data privacy and resilience without slowing down their application’s performance, workflows, or development cycle.
The benefits of data security offloading
Encrypting and decrypting data is CPU-intensive. Any computer dealing with encryption processes can become bogged down. Encryption also requires additional resources and planning around key management and key rotation, increasing the complexity of data workflows for applications.
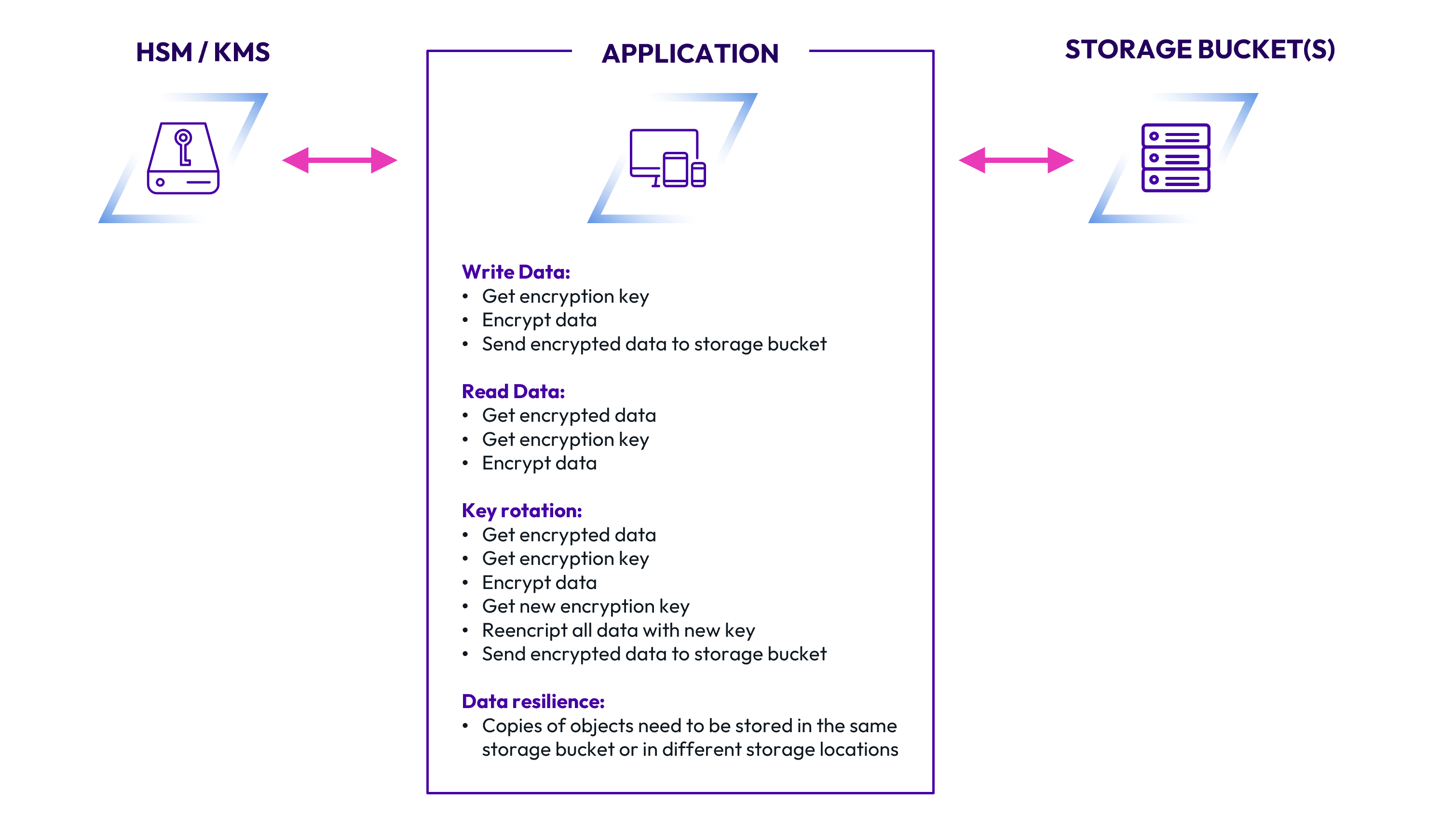
Beyond encryption management, application teams usually need to design processes for every read or write operation, for key management, and for hardware security modules. Data resilience is also a concern, as teams need to ensure their application can read and write data even during outages and other disruptions.
Here's a high-level overview of all the data security tasks that most application teams will need to implement.
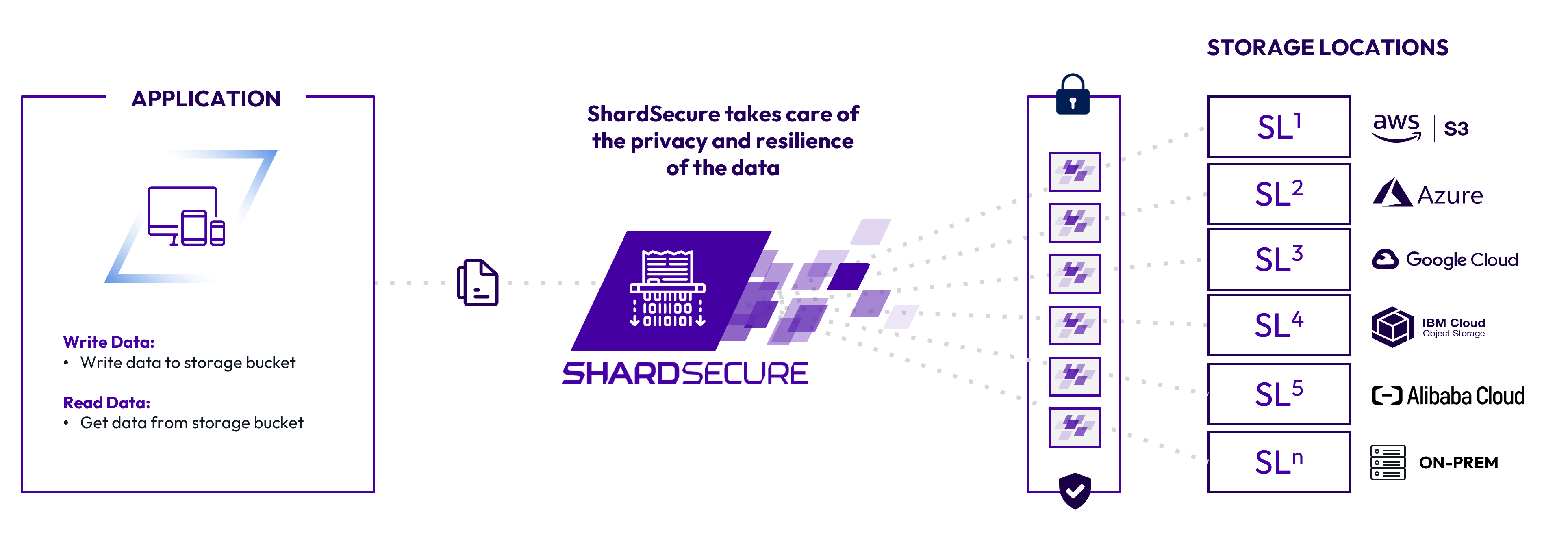
When data security offloading is implemented, on the other hand, application teams no longer need to worry about data protection. The application only needs to perform read/write operations to process data; no additional steps are necessary. All necessary security processes are built into the data security offloading solution.
As a result, data security offloading offers excellent benefits:
- Boosts application delivery timeframes.
- No performance hit on your applications.
- Easy to implement.
- Enhances the resilience of data.
- Auto-scaling during the peak hours of data processing.
- Application doesn’t need to support key rotation.
Any owner of an application that handles lots of encrypted data should consider data security offloading to free up engineering resources and help their team focus on their primary tasks.
Microsharding: a data security offloading solution
One way to handle data security offloading is through microsharding. Our solution uses unique high performance mechanisms to process data without a performance hit. With features like self-healing data, data integrity checks, and virtual clusters, we support strong data privacy and data resilience — all while avoiding any significant performance hit to your application.
Ensuring that data remains secure can be costly in terms of planning, development, and processing power. Data security offloading through ShardSecure can alleviate the workload for busy application teams and provide greater security to ward off malicious attacks.
To learn more about how we can help with data security offloading, contact us today — or take a look at our FAQs and solution briefs.







