There’s no doubt cloud adoption is becoming ubiquitous.
The datasets and workloads that have been migrated to cloud versus those that are still on premises may vary from organization to organization, but the total percentage of data making its way to cloud is only increasing. Recent survey figures such as Oracle and KPMG’s Threat Report cite a 3.5x increase in the number of organizations who now house over 50% of their data in cloud between 2018 and 2019, and growing.
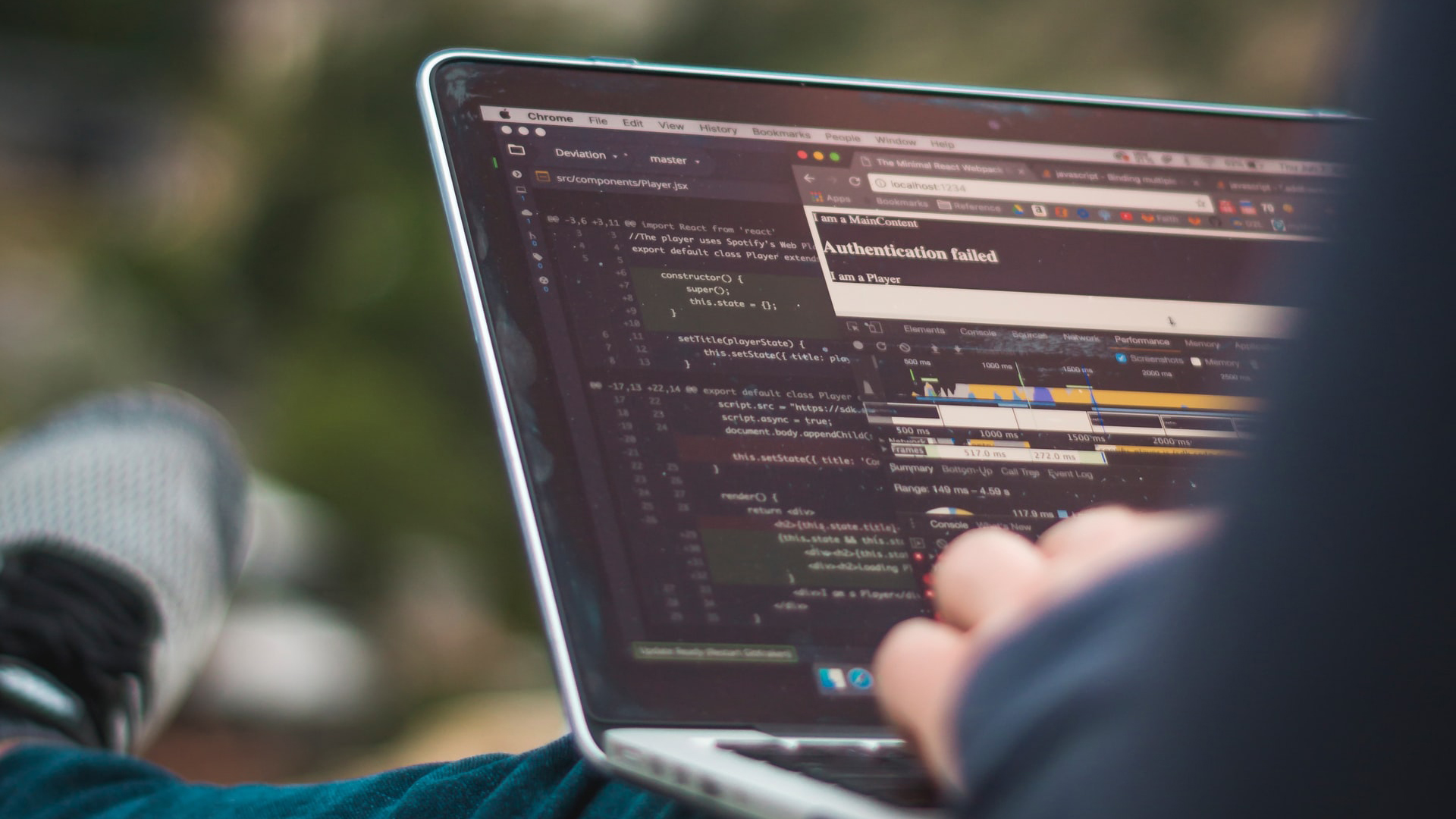
Tools that make deploying and migrating to the cloud easier than ever have been a key factor in its rapid adoption. But as the number of serious security breaches rises in tandem with cloud adoption, organizations, industry experts and customers’ whose data has been compromised are beginning to question whether cloud’s rapid on-ramps come with sufficient guard rails for its broad user base. In the “shared security responsibility model” of the cloud, it can be difficult to determine where the cloud provider’s responsibility ends and that of the cloud user begins.
Who should be held responsible for cloud security breaches may be up for debate, but there is no question as to what causes the majority of those incidents. Far and away, human error typically referred to as “cloud misconfigurations” were the leading cause of data breaches in 2019, as reported by the Cloud Security Alliance.
That figure, coupled with the fact that 82% of cloud users report experiencing a security event due to confusion over the shared security responsibility model, make it clear that the best security strategy is one that provides cloud users (and their organizations) more autonomy over the security of the data they’re moving to the cloud.
The most effective way to secure the data itself is to render it completely unreadable to would-be hackers. Through Microsharding™, organizations chunk formerly sensitive data into fragments tiny enough to break the atomic unit of value before it is migrated to the cloud. Data can be dispersed to multiple locations, including multiple cloud providers, and can be poisoned with false shards to further pollute data fragments.
Data fragments can only be reassembled to users with accurate credentials using pointers in the ShardSecure engine. Through Microsharding, ShardSecure desensitizes data in the cloud such that even if it is exposed due to a misconfiguration, it remains unreadable and therefore of no value to would-be hackers.
If, for example, an AWS S3 bucket is left unsecured, as has been the case in many of today’s most notable breaches, the data exposed would not be discernable in any way to would-be hackers even if the bucket itself was discovered. And the benefit of Microsharding data isn’t limited to avoiding a nasty security headline.
Storing sensitive data in the cloud can introduce millions of dollars in compliance fees, even more in damages and potential loss of business revenue caused by client mistrust. For organizations that have yet to migrate to the cloud for those very reasons, ShardSecure provides a clear path to cloud adoption by drastically reducing the risk associated with storing data there.
In blogs and industry conversation, the debate may continue about cloud’s burden of responsibility as it pertains to misconfigurations. However, security-conscious organizations need only look at the estimated $300 million dollar fallout faced by Capital One, the estimated $234 million dollar cost of the British Airline breach, or countless other cyber security fallout expenses incurred by organizations across the globe to understand the risk of cybersecurity vulnerability is tangible.
Rather than waiting on a cloud expert to perfectly configure data in the cloud, taking a proactive approach to securing the data itself is an effective strategy whether you store data on-premises, with one cloud provider or many.